Throughout our testing blueprint series, we’ve explored how testing serves as a strategic bridge between technical functionality and business adoption. We’ve examined how meticulous planning creates the foundation for successful testing, how masterful execution transforms testing from verification to discovery, and how stress testing ensures systems perform under real-world pressure. Now we turn to our final critical dimension: security testing—the protective shield that safeguards your digital transformation from an increasingly hostile landscape.
In an era where data breaches cost organizations an average of $4.2 million per incident and can irreparably damage trust, security cannot be an afterthought. The most effective organizations recognize that security isn’t something you add to a system—it’s something you build into its very foundation through deliberate design and methodical validation.
Beyond Functionality: The Security Imperative
If functional testing examines whether a system works as intended and stress testing validates whether it performs under pressure, security testing investigates whether it can protect itself and its data from those who would exploit it for malicious purposes.
The rise of sophisticated cyber threats, coupled with increasingly stringent regulatory requirements, has transformed security testing from a specialized technical concern into a strategic business imperative. Organizations now recognize that security vulnerabilities represent not just technical flaws but existential business risks.
What Questions Does Security Testing Resolve?
Effective security testing addresses several critical questions that other testing approaches cannot answer:
How vulnerable is the system to deliberate attacks and exploitation?
Are sensitive data and critical functionalities adequately protected?
Do security measures balance protection with usability?
Does the system comply with relevant security standards and regulations?
These questions transform security testing from a technical checkbox into a comprehensive risk management strategy—identifying and mitigating threats before they can materialize as business-damaging incidents.
Why Security Testing Matters: The Protection Gap
Here’s a sobering reality that experienced technology leaders understand: The most catastrophic security breaches often occur in systems that passed all functional tests flawlessly. The culprit? A fundamental disconnect between functional correctness and security resilience.
Consider a healthcare organization that implemented a new patient portal after extensive functional testing. Every feature worked perfectly, providing seamless access to medical records and appointment scheduling. But inadequate security testing missed a critical API vulnerability that allowed unauthorized access to patient data. The resulting breach exposed thousands of medical records, triggered regulatory penalties, and severely damaged patient trust.
Contrast this with a financial institution that incorporated security testing from the earliest design phases. Their “security by design” approach identified and remediated potential vulnerabilities throughout development. When targeted by sophisticated attackers, their system successfully repelled the intrusion—preserving both customer data and organizational reputation.
The difference wasn’t in the quality of coding or the thoroughness of functional testing—it was in recognizing that security must be engineered into systems from their inception, not added as an afterthought.
Security by Design: The Protective Approach
The most effective organizations approach security testing not as a final verification step but as an integral part of their development methodology—what we call “security by design.” This approach weaves protective considerations throughout the development lifecycle rather than treating them as post-development checks.

Figure 1: Security Testing Approach
This diagram illustrates the “security by design” approach, showing the cyclical flow from defining security requirements through architecture analysis, threat profiling, test planning, and execution. The bottom section displays the seven types of security testing that provide protection across different vulnerability dimensions. This systematic approach ensures that security isn’t merely tested but designed into the system from its foundation.
This protective cycle follows key phases that align security with development:
1. Define Security Requirements: Protection as a First-Class Concern
Traditional approach: Functional requirements dominate, with security treated as vague compliance checks.
Strategic approach: Security requirements are defined with the same precision as functional requirements, specifying:
- Data protection needs based on classification and sensitivity
- Authentication and authorization requirements for different user roles
- Audit and traceability expectations for sensitive operations
- Compliance obligations (regulatory, industry, contractual)
- Threat models specific to the business context
- Recovery and resilience expectations after security incidents
This precision transforms security from an ambiguous “should be secure” expectation to concrete, testable criteria that guide both design and validation.
2. Create and Analyze Architecture: Building SecurityIntothe Foundation
Once security requirements are established, they must inform the fundamental architecture of the system—ensuring that protection is built into the foundation rather than applied as a surface treatment.
Architectural security analysis includes:
- Data flow mapping to identify exposure points
- Trust boundary identification and validation
- Authentication and authorization frameworks
- Encryption approaches for data at rest and in transit
- Integration security across system boundaries
- Logging and monitoring frameworks
This architectural perspective ensures that security is woven into the system’s structure rather than applied as an afterthought—creating protection that is both more effective and more efficient.
3. Define Threat Profile: Understanding What You’re Protecting Against
Effective security testing is targeted—focusing on the specific threats most relevant to your business context rather than generic vulnerabilities. This targeting emerges from a detailed threat profile.
Comprehensive profiles address:
- External attack vectors specific to your industry
- Internal threat scenarios based on access patterns
- Data exfiltration risks based on information value
- Service disruption vulnerabilities and business impacts
- Compliance violation scenarios and their consequences
- Emerging threat patterns in your technology landscape
This threat-centered approach ensures that security testing identifies vulnerabilities that actual attackers would exploit rather than theoretical weaknesses with minimal risk.
4. Develop Test Plan and Tools: Methodical Protection Validation
Security testing requires different approaches and tools than functional testing—specialized techniques that reveal vulnerabilities rather than verify features. The test plan defines which security testing types to apply and how to orchestrate them for comprehensive coverage.
Effective security test plans include:
- Selection of appropriate testing types based on risk profile
- Definition of testing scope and boundaries
- Identification of specialized tools and techniques
- Clear delineation between simulated and actual exploitation
- Provisions for sensitive finding management
- Coordination with business continuity planning
This specialized planning ensures that security testing systematically addresses the full spectrum of potential vulnerabilities rather than providing false confidence through incomplete coverage.
5. Layered Security Testing: Comprehensive Protection Across Dimensions
Unlike functional testing, which follows relatively standardized approaches, security testing encompasses multiple specialized techniques—each designed to identify different types of vulnerabilities. The most effective security testing strategies employ a layered approach, combining multiple test types to create comprehensive protection.
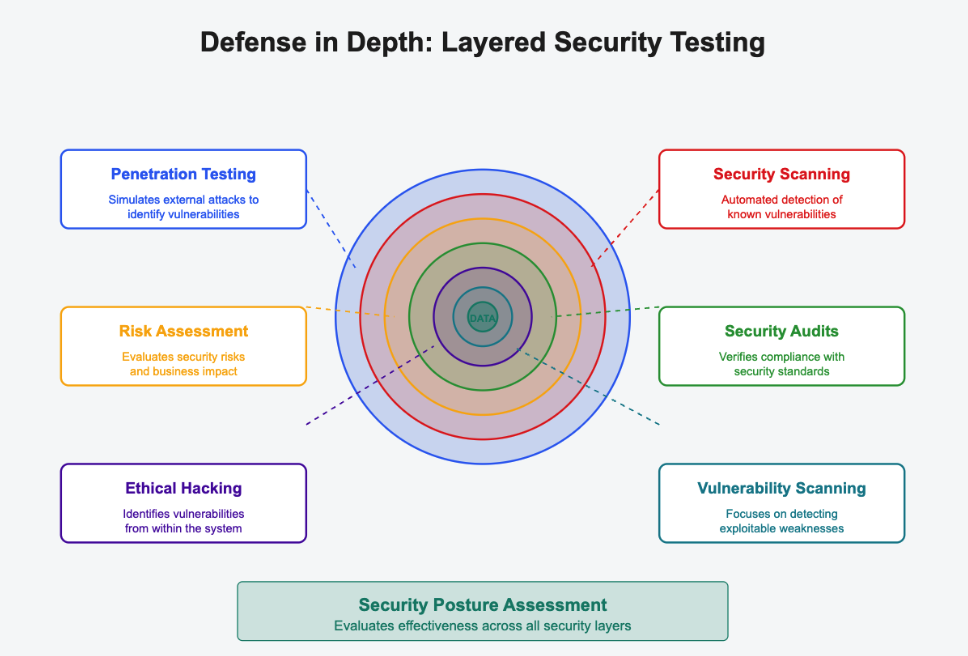
Figure 2: Security Testing Layers
This visual illustrates the defense-in-depth model used in comprehensive security testing. Each concentric circle represents a different layer of security protection, with descriptions clearly labeled on both sides. The outermost layers like penetration testing simulate external attacks, while inner layers such as ethical hacking address internal vulnerabilities. At the protected core sits the sensitive data, surrounded by multiple defensive barriers. This multi-layered approach ensures that if one security measure is compromised, additional protective layers remain in place to shield critical assets from harm. The bottom section shows how security posture assessment evaluates effectiveness across the entire security ecosystem.
Security Testing Types: Comprehensive Protection Across Dimensions
Unlike functional testing, which follows relatively standardized approaches, security testing encompasses multiple specialized techniques—each designed to identify different types of vulnerabilities.
The following table outlines seven key testing types that provide comprehensive protection:
| Security Testing Type | Description | When to Use |
| Penetration Testing | Simulates external attacks to find potential loopholes for accessing the application and data | For externally accessible systems containing sensitive data or critical functionality |
| Security Scanning | Automated or manual scan of the network and application to find potential weaknesses and provide solutions | Early in development to identify known vulnerabilities in code and configurations |
| Vulnerability Scanning | Automated system scanning to detect weaknesses | Regularly throughout the development lifecycle and in production |
| Security Risk Assessments | Testing and observing security risks, then categorizing based on probability, business threat, and complexity | When evaluating overall security posture and prioritizing remediation efforts |
| Security Audits and Reviews | Internal testing of the application and code to identify issues against requirements and security standards | For compliance validation and to ensure adherence to security policies |
| Ethical Hacking | Similar to penetration testing, except attacks are performed from within the system to detect security flaws | When internal threats are a significant concern or to validate internal security controls |
| Posture Assessment | Combines security risk assessments, security scanning, and ethical hacking to provide an overall security view | When a comprehensive evaluation of security readiness is needed across dimensions |
This multifaceted approach ensures that security testing identifies vulnerabilities across the full spectrum of potential weaknesses—providing comprehensive protection rather than isolated security measures.
Security Testing in Action: Beyond Theoretical Vulnerabilities
While security testing involves specialized techniques, its ultimate value comes not from identifying theoretical vulnerabilities but from revealing practical risks that could impact business operations. Effective security testing connects technical findings to business implications.
Consider these examples of how different security testing approaches reveal distinct types of vulnerabilities:
Penetration Testing: Revealed that a seemingly minor file upload functionality could be exploited to execute malicious code, potentially compromising an entire system.
Security Scanning: Identified outdated libraries with known vulnerabilities that created exploitable weaknesses despite custom code being secure.
Vulnerability Scanning: Detected misconfigurations in cloud services that inadvertently exposed sensitive data to public access.
Security Risk Assessment: Recognized that separation of duties was inadequate in a financial system, creating fraud opportunities despite strong technical controls.
Security Audit: Discovered that encryption key management practices violated regulatory requirements, creating compliance risks despite data being encrypted.
Ethical Hacking: Demonstrated that social engineering combined with technical exploits could bypass seemingly robust security measures.
Posture Assessment: Identified organizational security blind spots where responsibilities were unclear, creating vulnerability gaps between systems.
These real-world examples demonstrate how comprehensive security testing reveals vulnerabilities that individual techniques might miss—providing protection across the full spectrum of potential risks.
Integrating Security Testing Into the Development Lifecycle
For security testing to be most effective, it must be integrated throughout the development lifecycle rather than applied only at its conclusion. This integration shifts security from a gating function to an enabling capability.
Traditional approach: Security testing occurs as a final verification step, often identifying issues that require costly reworking.
Strategic approach: Security validation occurs continuously throughout development:
- Requirements phase: Security requirements defined alongside functional needs
- Design phase: Threat modeling and architectural security analysis
- Development phase: Secure coding practices and automated security scanning
- Testing phase: Layered security testing approaches
- Deployment phase: Final security validation and continuous monitoring
This integrated approach transforms security from a development bottleneck into a quality enabler—identifying issues when they’re least expensive to fix while building security expertise throughout the organization.
Beyond Testing: Building a Security Culture
While security testing provides essential validation, true protection emerges from a fundamental shift in organizational thinking—from seeing security as a specialized technical function to recognizing it as a shared responsibility that permeates every aspect of development and operations.
This security culture manifests in several key principles:
| Security Principle | Traditional Approach | Security Culture Approach | Business Impact |
| Security Ownership | Security is the exclusive responsibility of specialized teams | Security is everyone’s responsibility, with specialized teams providing expertise | Reduced blind spots as all team members contribute to security awareness |
| Design Philosophy | Security is added to systems after functional design | Security requirements influence design decisions from inception | More effective protection with lower implementation costs |
| Vulnerability Response | Vulnerabilities trigger blame and defensive reactions | Vulnerabilities are viewed as learning opportunities with blameless postmortems | Faster identification and remediation as issues are reported without fear |
| Security Knowledge | Security expertise is concentrated in specialized roles | Basic security knowledge is widely distributed with specialized depth where needed | More effective protection as teams make security-conscious decisions throughout development |
This security culture transforms protection from a specialized function into a pervasive mindset—creating organizations where security becomes a natural aspect of how systems are conceived, built, and operated.
The Complete Testing Blueprint: Bringing It All Together
As we conclude our testing blueprint series, it’s important to recognize that these different testing dimensions—strategic foundation, planning and preparation, execution and communication, stress testing, and security testing—are not isolated activities but interconnected aspects of a comprehensive testing strategy.
The most effective testing approaches integrate these dimensions into a coherent whole:
- Strategic foundation defines why you’re testing and what success looks like
- Planning and preparation establishes how testing will be structured and resourced
- Execution and communication determines how testing is conducted and insights are shared
- Stress testing validates how systems perform under pressure
- Security testing ensures systems are protected from threats and vulnerabilities
Together, these dimensions create a testing strategy that validates not just whether systems work as designed, but whether they deliver sustainable business value in the complex reality of production operations.
Looking Beyond: The Continuous Testing Journey
While our blueprint series has provided a comprehensive framework for testing, it’s important to recognize that testing is not a one-time activity but a continuous journey that evolves alongside your digital transformation.
The most mature organizations approach testing as an ongoing capability that adapts to changing business needs, emerging technologies, and evolving threats. This continuous approach ensures that testing remains relevant and effective throughout the transformation lifecycle—from initial concept through ongoing operation and enhancement.
As you apply the testing blueprint to your own transformation efforts, remember that the goal isn’t perfect testing but effective testing—validating what matters most to your business while building the capabilities needed for sustainable success.
This article concludes our “Testing Blueprint” series—exploring how strategic testing approaches bridge technical quality and business success.
How does your organization approach security testing? Have you experienced the shift from security as an afterthought to security by design? Share your experiences in the comments below.
